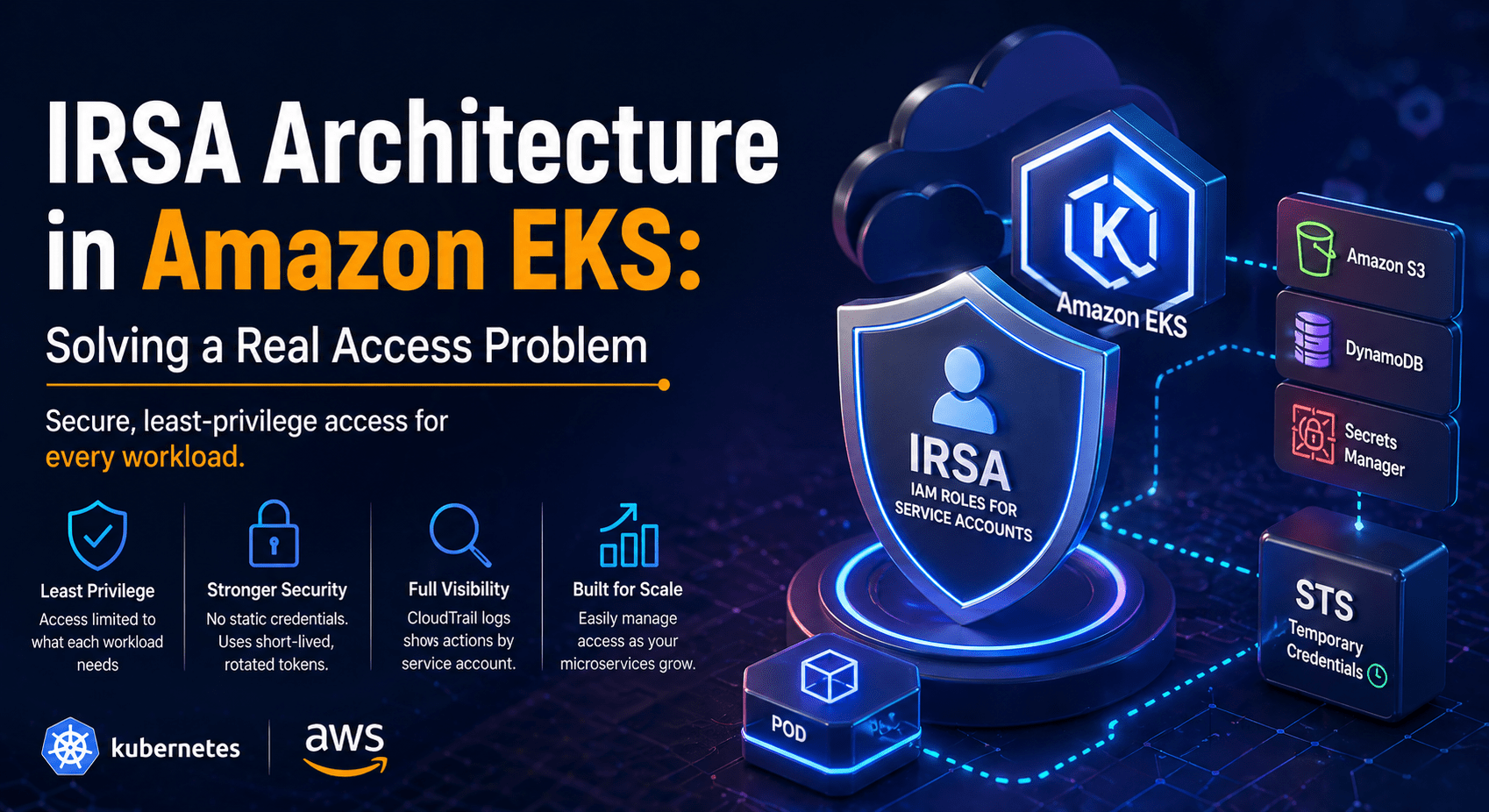
IRSA Architecture in Amazon EKS: Solving a Real Access Problem
Introduction When using Kubernetes, such as Amazon EKS, apps rarely run on their own. Most workloads require interaction with AWS services such as S3, DynamoDB, or Secrets Manager. At first glance, it looks like giving that access is easy. In practice, it quickly becomes a very important security and design issue. The problem isn’t just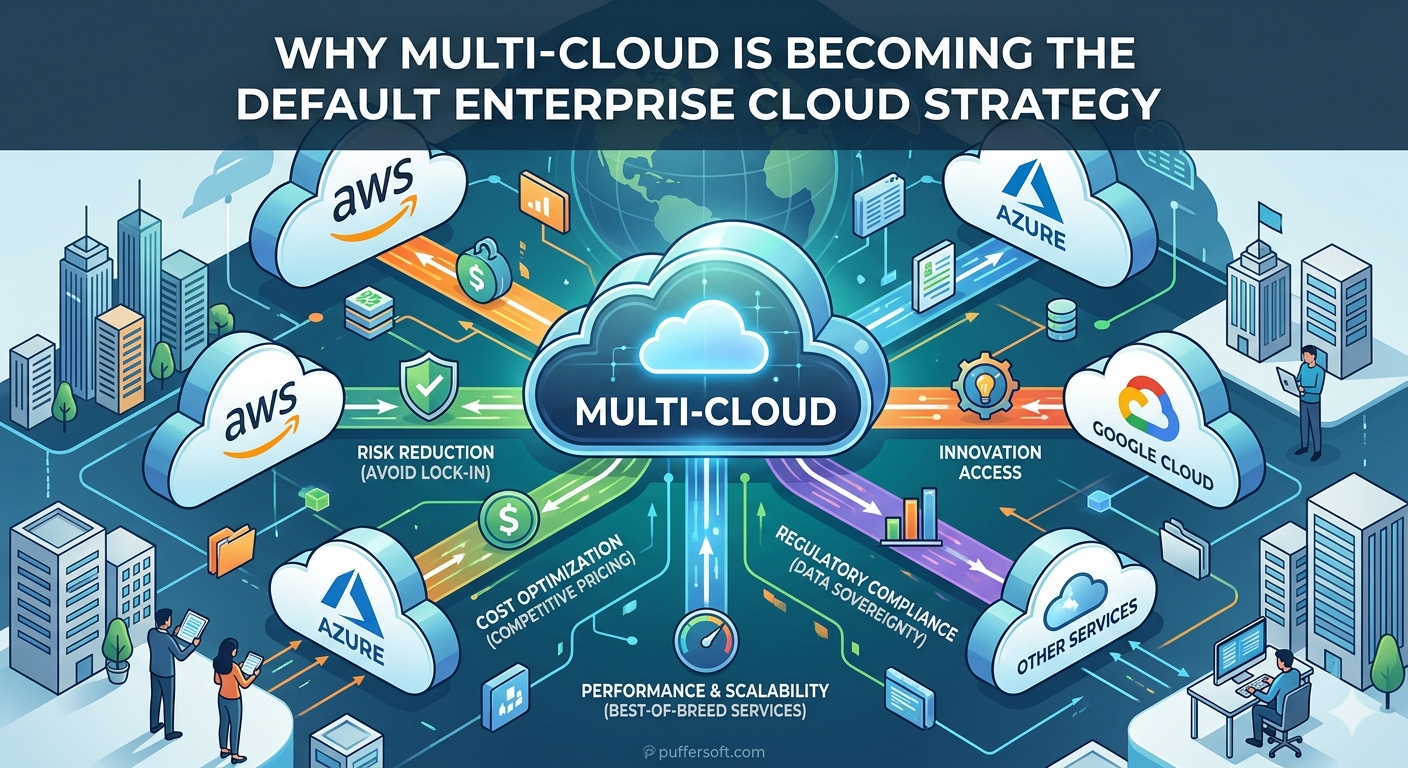
Why Multi-Cloud Is Becoming the Default Enterprise Cloud Strategy
The Shift Beyond Single-Cloud Thinking In the last ten years, companies have evolved from trying out cloud computing to using digital transformation throughout their business. At the beginning of this journey, many businesses adopted a single vendor to host their cloud infrastructure. A company would choose one cloud vendor to work with, typically either AWS